Chapter 7 - Section 7.4
advertisement
7.4 Firewalls Network Security / G.Steffen 1 In This Section What is a Firewall? Types of Firewall Comparison of Firewalls Types What Firewall Can-and Cannot Block Network Security / G.Steffen 2 What is a Firewall? A device that filters all traffic between a protected or “inside” network and a less trustworthy or “outside” network. It runs on a dedicated device It is an executable code, therefore an attacker could comprise that code & execute from the firewalls device. Its purpose is to keep a protected environment. Network Security / G.Steffen 3 Types of Firewalls 1 Packet Filtered Gateway It is the simplest and in some situation the most effective. It controls access to packets on the basis of packet address. Network Security / G.Steffen 4 Types of Firewalls 2 Stateful Inspection Firewall It maintains state information from one packet to another in the input stream. It also tracks the sequence of packets & conditions from one packet to another to thwart an attack. Filter Screening Outside Addresses Network Security / G.Steffen 5 Types of Firewalls 3 Application Proxy It suns pseudo-applications Packet filters look only at the header of packets, passing anything to port 25. Application proxy gateway (bastion host)- a firewall that simulates the proper effects of an application so that the application receives only requests to act properly. A proxy gateway intrudes in the middle of the protocol exchange Network Security / G.Steffen 6 Types of Firewalls 4 Guards It is a sophisticated firewall Similar to proxy firewall, receives protocol data units, interprets them and passes them. Personal Firewalls It is an application program that runs on a workstation to block unwanted traffic, usually from the network. It is configured to enforce some policies. It sums on the computer it is trying to protect. Network Security / G.Steffen 7 Comparison of Firewall Types Packet Filtering Stateful Inspection Application Proxy Guard Personal Firewall Simplest More complex More complex Most complex Simple See only addresses & service protocol type Can see either addresses or data See full data portion of packet Sees full text of See full data communication portion of packet Auditing difficult Auditing possible Can audit activity Can audit activity Network Security / G.Steffen Usually does audit activity 8 What Firewall Can-and Cannot Do Firewall It must be configured properly It only protects the perimeter of its environment. They are targets for penetrators It exercises only minor control over the content admitted to the inside. It does not protect data outside the perimeter It alone cannot secure an environment Network Security / G.Steffen 9


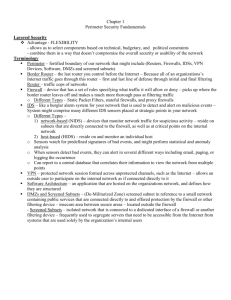



![Firewalls [electronic resource] : a complete guide / Marcus Gonçalves](http://s3.studylib.net/store/data/008069622_1-389c320965cbef1fbef3bfdf9967476c-300x300.png)