Chapter 4-1
advertisement
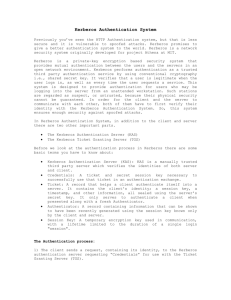
Chapter 4 – Protection in General-Purpose Operating Systems Section 4.1 Protected Objects and Methods of Protection Section 4.2 Memory and Address Protection 4.3 Control of Access to General Objects 4.4 File Protection Mechanisms In this Section Memory Protection Fence Base/Bound Segmentation Page Segmentation/Page Object Control Directory Access Control List Access Control Matrix Kerberos File Protection Mechanisms Protection in General-Purpose OS Some program are insecure just based upon the nature of the program Problem Children: Operating Systems and Databases (require access by many different “privileged” users) OS General Goal: Controlling Shared Access and Interface. OS Function (each have much security concern) Access Control Identification and Credentials Information flow Need to separate levels of security for particular users Projected Objects and Methods of Protection In the beginning there was no OS…. Programs were just inputted – cards/switches and the human hand were the OS Early OS was just a utility called an executive and only handled a single user - system resources managed by user Multiprogrammed OS allowed for more than one user – system resources managed by the monitor Early day protection was easy – you protected the user from themselves but today you must protect all users of an OS from each other and Malory Protected Objects In a multiprogram environment many objects need protection: Memory Sharable I/O devices Serially/Parallel reusable I/O devices Sharable programs and subprocedures Networks Sharable Data Notice the single correlation of all these “Shared” Security Methods of Operating Systems Basis of protections is separation (keeping user objects away from other users) Methods of Separation: Physical – nothing shared Temporal – operating things a different times Logical – running together but can’t access each other Cryptographic - running together but concealed Levels of Share Protection Do not Prevent – no protection when procedure are being run at different times Isolate – running concurrently but aware of each other; separate space, objects and files Share all or share nothing – owner of objects declare it public or private (all or none) Share via access limitation – each user is checked for access availability of an object Share by compatibilities- dynamic creation of shared objects Limit use of an object- user has varying access to an object Each has a varying level of granularity - Greater granularity creates greater access control Fence/Fence Register – Memory and Address Protection Simplest of all protection Confine the user to one side of a boundary Used to separate OS and Program (wasteful use of space) Protects a user from an OS but not a user from another user Base/Bound Register Created for a multiuser environment Base Register – variable fence register (lower bound) Bound Register – the upper address limit Tagged Architecture In base/bound, it is an all or nothing on the sharing of data. It is hard to manage because of it contiguous data space. Tagged Architecture- every word of machine memory has one extra bits to identify access right Segmentation Segmentation – notion of dividing a program into separate pieces – each has a logical unity Code for a procedure, sub procedure, array Unlimited number of base/bound registers <name, offset> Segmentation Segment Address Table is created for each program used to determine the true memory address of an instruction or data Paging Program divided into equal size chunks called pages and inserted into page frames; <page, offset> Unlike segmentation all pages are the same size removing most fragmentation slight sifting of data can cause security problems Paging-Segmentation Combing the benefits of Paging and Segmentation Control of Access to General Object Objects to Protect Memory File or data on storage device Executing program in memory Directory of files Hardware device Data structure Tables of the OS Instructions, privileged instructions Passwords - Authentication The protection mechanism Goals to Protecting Objects Check every access – able to revoke a right to an object Enforce least privilege – user/object should have access to the smallest number of objects necessary to perform some task Verify acceptable usage – Not just access an object but check to see if its use of the object is acceptable Directory Access Each user has a list to determine access to an object Problem – large lists, revocation of access, and multiple entries of the same name Access Control List A single list for each object Lots of advantages over Directory Access Access Control Matrix Each row represents a subject and each column represents a object. Each entry is the set of access rights Table 4-1 in textbook Capability Capability is an unforgettable token that gives rights to an object Sometimes a user must have a ticket; Domain useage Kerberos Kerberos is an implementation of a ticket based system with authentication Authentication Server (AS) – authenticates the user Ticket Granting Server (TGS) – provides the ticket Key Distribution Center (KDC) – is made up of the AS and TGS File Protection Mechanisms All-None System (Unacceptable) Lack of Trust Too Course Rise of Sharing Complexity File Listings Group Protection (has problems) Group Affiliation Multiple Personalities All Groups Limited Sharing