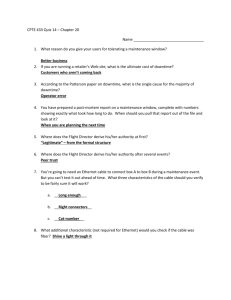
Chapter 20
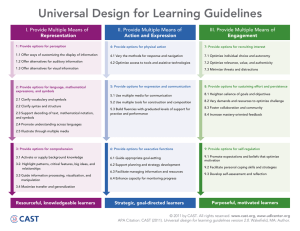
advertisement
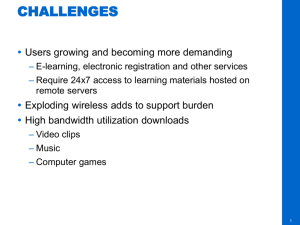
Management, Monitoring, and Optimization Chapter 20 Networking Essentials Spring, 2013 Managing Documentation Necessary Evil – Electronic copy you can easily access and modify – Hard copy in a binder that you/others can access Why hard copy? – Third electronic copy off-site (in case of fire, etc.) Schematics and Diagrams Wiring Schematic – EIA/TIA 568B – EIA/TIA 568A – Two notes on page 704 – Label that cable! Physical Network Diagram Logical Network Diagram Baselines For servers and clients – Processor – Memory – Hard disks – NICs / switches / routers Policies, Procedures, Regulations Policies – – How network is configured – How users are expected to behave Procedures – – Precise steps to follow in a given situation Regulations – – Rules imposed on your organization by an outside agency Network Monitoring and Logging Packet Sniffers Network Monitor from Microsoft Event Viewer (p. 715) – Application – Security – System Reasons to Optimize Networks Latency Sensitivity High bandwidth applications – VoIP – Video applications Uptime – what is reasonable? How to Optimize Performance Quality of Service (QoS) – – – – – Delay Dropped packets Delivery error Jitter Out-of-order delivery – Eight levels defined on page 719 How to Optimize Performance Traffic Shaping – Load Balancing – High Availability – – Planned downtime vs. unplanned downtime – Uptime vs. availability Caching Engines – Fault Tolerance I’m outta here! All Done! Way to go! Rrrrrrrrrr!! I found this thoroughly enjoyable!