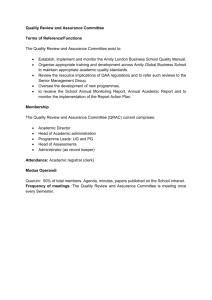
INFORMATION ASSURANCE INFORMATION SECURITY 01 02 03 04 INFORMATION PROTECTION CYBER SECURITY 05 INFORMATION ASSURANCE 06 INFORMATION ASSURANCE 07 INFORMATION ASSURANCE 08 INFORMATION ASSURANCE: 09 INFORMATION ASSURANCE 10 INFORMATION ASSURANCE: : Business Enabler : Cost Effective and Cost Beneficial : Robust Approach 11 : Protects the Fabric of an Organization’s Systems Shared Responsibilities INFORMATION ASSURANCE: Restricted by Social Obligations Reassessed Periodically INFORMATION ASSURANCE is the overarching approach for identifying, understanding, and managing risk through an organization’s use of information and information systems. As noted in the MSR model, information assurance is concerned with the life cycle of information in an organization through the objectives of maintaining the following services or attributes: CONFIDENTIALITY assures that the unauthorized parties do not have access to information. The information which is being transmitted must be encrypted. Only those who are authorized can decrypt and access this information. INTEGRITY assures that the information remains in its original state, meaning the system should safeguard data's accuracy and completeness. Integrity ensures that unauthorized individuals do not tamper with or modify the information. AVAILABILITY ensures that the authorized parties have easy and timely access to the information system. This pillar ensures the system remains robust and fully functional even during adverse conditions. It involves protection against threats that can block access to the information system. AUTHENTICATION ensures the validity of a transmission of a message or the verification of a party's authorization to receive specific information. It prevents impersonation and requires confirmation of the identities of the party before giving access to the information system and resources. NON-REPUDIATION ensures that the sender is provided with proof of delivery and the receiver is provided with proof of sender's identity. This attribute assures the sender of data is provided with proof of delivery and the recipient is provided with proof of the sender's sending the message so that neither can deny sending or receiving data, respectively. MUST REMEMBER about Info. Assurance! • Information assurance includes all information an organization may process, store, transmit, or disseminate regardless of media. Thus, information on paper, on a hard drive, in the mind of an employee, or in the cloud is considered to be “in scope.” • Information security, information protection, and cybersecurity are subsets of information assurance. INFORMATION SECURITY covers the tools and processes that organizations use to protect information. This includes policy settings that prevent unauthorized people from accessing business or personal information Information security is a subdomain of information assurance. As noted in the MSR model, information security focuses on the CIA triad. The CIA Triad— Confidentiality, Integrity, and Availability—is a guiding model in information security. CONFIDENTIALITY Prevents sensitive information from reaching wrong people while making sure that the right people can use it. INTEGRITY Maintain information consistency, accuracy, and trustworthiness of information over it life cycle. AVAILABILITY Ensures that the information is available when it is needed. MUST REMEMBER about Info. Security! • Like information assurance, information security includes all information an organization may process, store, transmit, or disseminate regardless of media. Thus, information on paper, on a hard drive, in the mind of an employee, or in the cloud is considered in scope. • Information protection and cybersecurity are subsets of information security. INFORMATION PROTECTION Information protection is best viewed as a subset of information security. It is often defined in terms of protecting the confidentiality and integrity of information through a variety of means such as policy, standards, physical controls, technical controls, monitoring, and information classification or categorization. MUST REMEMBER about Info. Protection! • Like information security, information protection includes all information an organization may process, store, transmit, or disseminate regardless of media. Thus, information on paper, on a hard drive, in the mind of an employee, or in the cloud is considered in scope. • Some laws, regulations, and rules specifically cite information protection as a requirement for sensitive information such as personally identifiable information and personal health information. CYBERSECURITY Cybersecurity is a relatively new term that has largely replaced the term computer security. Cybersecurity is used to describe the measures taken to protect electronic information systems against unauthorized access or attack. Cybersecurity is primarily concerned with the same objectives of information security within the scope of electronic information systems’ CIA. MUST REMEMBER about Cybersecurity! • Cybersecurity is primarily focused on the protection of networks and electronic information systems. Other media such as paper, personnel, and in some cases stand-alone systems that rely on physical security are often outside the scope of cybersecurity. • Cybersecurity often focuses on the vulnerabilities and threats of an information system at the tactical level. System scanning, patching, and secure configuration enforcement are common foci of cybersecurity. • Intrusion detection and incident response and other functions commonly run from a security operations center (SOC) are often identified as cybersecurity functions. INFORMATION ASSURANCE: Business Enabler Ensures business confidence and acts as a competitive advantage rather than an obstacle assists in achieving organization's vision and mission by protecting its critical assets and resources INFORMATION ASSURANCE: Protect the Fabric of an Organization’s System Information systems provide the interconnecting elements of effective management of organizations. If, however, the information system does not demonstrate the security elements of the MSR model, management cannot make informed decisions. Information assurance is a shared responsibility and involves not only the IT organization and other employees. Information assurance should be incorporated into the current management strategy system and requires participation from all functional units. INFORMATION ASSURANCE: Cost Effective and Cost Beneficial Cost-effective: Information assurance refers to implementing measures that provide the necessary level of protection while minimizing the cost of implementation and maintenance. In other words, it is about achieving the desired level of security while keeping the costs low. Cost beneficial: A thorough analysis of the costs and benefits of information assurance may examine either quantitative or qualitative aspects to ensure investment on controls meet expectations. Security investments should take into consideration the cost of designing, implementing, and maintaining the controls; the values of information assets; the degree of dependency on the information systems; and the potential risk and impact the organization is likely to face. Investing in information assurance is both a horizontal and vertical effort. INFORMATION ASSURANCE: Shared Responsibilities Security is a team effort and a shared responsibility. No single individual or group—from development to operations to security—carries the burden of security in totality. Shared responsibility means holding everyone accountable for information security best practices (shutting down laptops, closing office doors, maintaining good passwords, etc.) INFORMATION ASSURANCE: Robust Approach Information assurance requires a complete and integrated approach that considers a wide range of processes. This comprehensive approach extends throughout the entire information life cycle. Security controls operate more effectively in concert with the proper functioning of other business process controls INFORMATION ASSURANCE: Reassessed Periodically To maintain the security of their information systems and minimize the risk of negative impacts on their mission, organizations must continuously monitor their controls, conduct regular assessments, and ensure information assurance is incorporated into change and configuration management processes. This will alert management to new risks and the condition of the information systems, data, and networks that may have a negative impact on the mission of the organization. INFORMATION ASSURANCE: Restricted by Social Obligations Organizations must consider social obligations in the implementation of security controls. Organizations should balance the rights and desires of the organization versus the rights of organizational employees and customers. This involves understanding the security needs of information owners and users. Expectations and policies may change concerning the suitable use of security controls. Organizations need to balance between security risks they are willing to accept versus human rights or social factors. This can lead to solving issues such as security and the workplace privacy conflict. Employee monitoring and a bringyour-own-device (BYOD) policy are areas where social obligations and information assurance often require extensive analysis.