Common network diagnostic and configuration utilities A ‘toolkit’ for network users and
advertisement

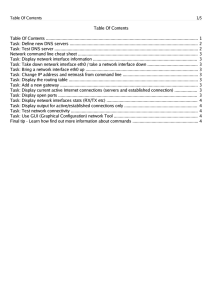
Common network diagnostic and configuration utilities A ‘toolkit’ for network users and managers when ‘troubleshooting’ is needed on your network Kudlick Classroom 08 09 10 15 04 05 06 07 01 02 03 16 17 18 19 11 12 13 14 20 28 29 30 24 25 26 27 21 22 23 lectern Each student workstation has two Intel PRO1000 Gigabit Ethernet Controllers; one is named ‘eth0’ and it is connected to a LAN switch that has a ‘gateway’ to the campus network and the Internet; the other is named ‘eth1’ and it is connected to a different switch which does not offer an Internet ‘gateway’ ‘hostname’ • This command will quickly show you the network name for your host machine (or will allow you to change that name if you possess the necessary authorization) • Example: $ hostname • This command works by calling a standard library function (e.g., ‘gethostname()’ ) that we’ll often be using in our own programs ‘ping’ • A standard UNIX tool for testing whether a particular host is reachable across an IP network – and if so, then how quickly? • Example: $ ping 138.202.171.14 • It also confirms that a Network Interface Controller is operating properly, and that a hostname can be ‘resolved’ to its address • Example: $ ping stargate.cs.usfca.edu ‘traceroute’ • A tool for determining what route is being taken by packets sent over an IP network • Example: $ traceroute cs.stanford.edu • This tool will report on each of the ‘hops’ between network ‘routers’ along a path to the specified destination, and the elapsed times for each ‘hop’ (in milliseconds) • (A similar tool for Linux is ‘tracepath’) ‘route’ • It lets users display current information in a host’s ‘routing table’ database -- and it lets a privileged user manipulate that info • Example: $ /sbin/route -n • The routing table’s entries tell the kernel’s networking subsystem how to deliver, or forward, or else discard, any IP-network packets that are being received by a NIC ‘tcpdump’ • This is a ‘packet decoding’ tool – it shows where a packet is coming from, where it is going to, as well as its size and its purpose • But it’s only available to a ‘privileged’ user • Example: $ sudo /usr/sbin/tcpdump –i eth0 • For an active interface on the internet, the volume of output normally produced is so intense as to overwhelm a human’s view! ‘netstat’ • It can show a lot of information about the current state of your host’s networking subsystem – such as routing-table entries, active connections, ports and protocols, or statistics for the active Network Interfaces • Example: $ netstat -i • It’s not a ‘privileged’ command – any user can execute Linux’s ‘netstat’ utility ‘whois’ • It’s queries an official Internet database to determine the current owner of a network domain name or host name • Example: $ whois 138.202.0.0 • It allows users to find out who they can contact in order to report any abuses or malfunctions that have been identified as originating from a particular IP-address ‘ifconfig’ • This program allows a user to view status information and statistics for any network interfaces which exist in your machine, or to modify the state of a network interface if you possess the necessary authorizations • Example: $ /sbin/ifconfig -a • With ‘sudo’ privileges, we will be able to make changes to our interfaces’ states ‘ftp’ • This offers a convenient command-line interface to the File-Transfer Protocol which is implemented on the Internet • Example: $ ftp hopper.usfca.edu • You will usually need to enter a password and a sequence of ftp-specific commands in order to ‘download’ (or ‘upload’) a file using this standard UNIX ‘ftp’ application ‘telnet’ • This program lets users communicate with remote servers using the ‘telnet’ protocol • Example: $ telnet rainmaker.wunderground.com 3000 • Of course, the remote host must allow the connection for specified port-number and for the user who is attempting to connect • System administrators often configure a network’s ‘firewall’ to reject telnet-requests Thanks, Alex! • Our System Administrator, Alex Fedosov, has kindly provided a list of several other networking utilities that he finds are very useful in managing the CS Department’s various local networks and its ‘gateways’ • Most of those tools are not mentioned by our textbook because they are mainly of use for specialized management tasks ‘nmap’ • This is a networking security port-scanner with lots of options and capabilities that a Network Administrator would find helpful for doing security-related troubleshooting • Example: $ nmap localhost ‘lsof’ • This utility lists a host’s open files and its network connections (i.e., ‘sockets’), and shows which processes are using them • Example: $ /usr/sbin/lsof • There are lots of command-line options (see the online manual: $ man lsof ) that can make the displayed information be more helpful for your specific purpose ‘host’ • This is a Domain Name Service ‘resolver’ allowing a user to find out the hostname for a particular Internet Protocol address • Example: $ host 138.202.1.15 • Notice that the order in which the numeric components of the host’s IP-address are shown in this program’s output has been reversed (bringing up the ‘endian’ topic) ‘arp’ • This utility displays information in a host’s ARP cache (Address Resolution Protocol) and allows a user to manipulate that info • Example: $ /sbin/arp Demo: ‘nicwatch.cpp’ • This is ‘packet sniffer’ that your Instructor has created for your use in studying how the network interfaces in our classroom machines are working, and for assistance in ‘debugging’ your own network programs • Example: $ nicwatch eth0 • You can redirect its screen-output to a file if you want to examine it more leisurely! In-class exercise #1 • Find out what IP-address is being used by your classroom workstation: $ ping hrn235xx • Now look at your workstation’s ‘routing table’ to see which interfaces are currently being used: $ /sbin/route -n • Then use the ‘ifconfig’ utility to assign an IPaddress to your machine’s secondary NIC (i.e., to the ‘eth1’ network interface) $ sudo /sbin/ifconfig eth1 192.168.1.xxx up • Did this cause any routing-table changes? In-class exercise #2 • Now that your secondary NIC is “up” and is using an IP-address on the 192.168.1.0 local area network, you can use ‘ping’ to see if other host are reachable on the LAN $ ping 192.168.1.yyy • In a separate window you can execute our ‘nicwatch’ utility while ‘ping’ is running: $ nicwatch eth1