CS475 – Networks Assignments Lecture 22 Chapter 6: Congestion Control and Resource Allocation
advertisement
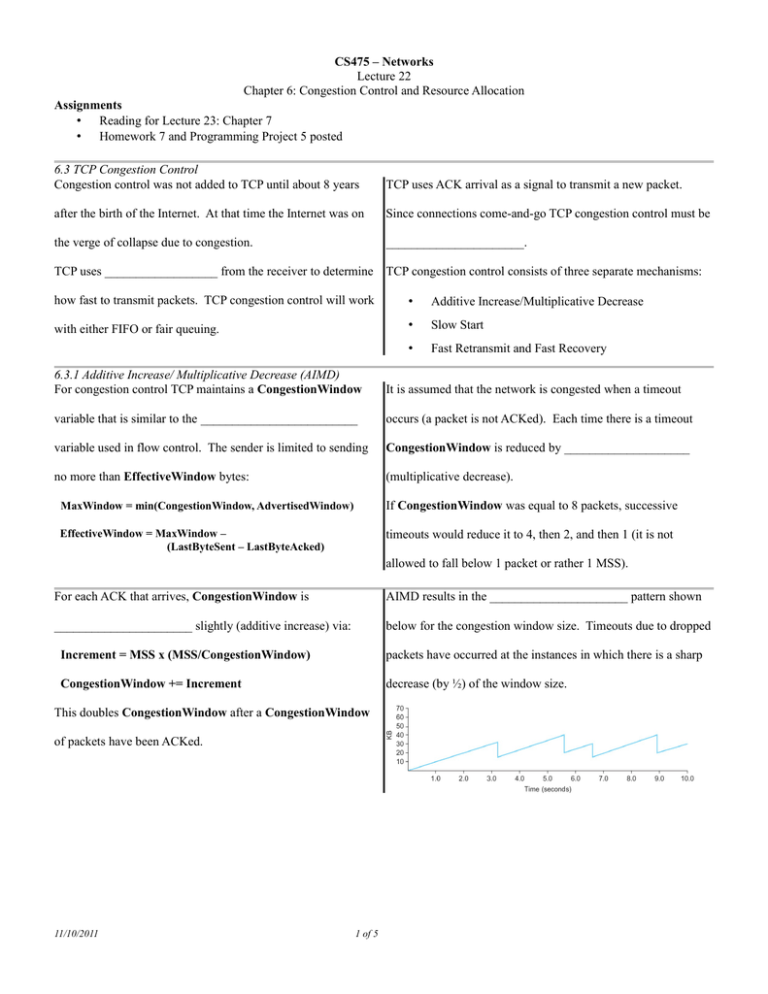
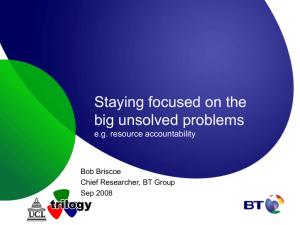
CS475 – Networks Lecture 22 Chapter 6: Congestion Control and Resource Allocation Assignments • Reading for Lecture 23: Chapter 7 • Homework 7 and Programming Project 5 posted 6.3 TCP Congestion Control Congestion control was not added to TCP until about 8 years TCP uses ACK arrival as a signal to transmit a new packet. after the birth of the Internet. At that time the Internet was on Since connections come-and-go TCP congestion control must be the verge of collapse due to congestion. ______________________. TCP uses __________________ from the receiver to determine TCP congestion control consists of three separate mechanisms: how fast to transmit packets. TCP congestion control will work • Additive Increase/Multiplicative Decrease with either FIFO or fair queuing. • Slow Start • Fast Retransmit and Fast Recovery 6.3.1 Additive Increase/ Multiplicative Decrease (AIMD) For congestion control TCP maintains a CongestionWindow It is assumed that the network is congested when a timeout variable that is similar to the _________________________ occurs (a packet is not ACKed). Each time there is a timeout variable used in flow control. The sender is limited to sending CongestionWindow is reduced by ____________________ no more than EffectiveWindow bytes: (multiplicative decrease). MaxWindow = min(CongestionWindow, AdvertisedWindow) If CongestionWindow was equal to 8 packets, successive EffectiveWindow = MaxWindow – (LastByteSent – LastByteAcked) timeouts would reduce it to 4, then 2, and then 1 (it is not allowed to fall below 1 packet or rather 1 MSS). For each ACK that arrives, CongestionWindow is AIMD results in the ______________________ pattern shown ______________________ slightly (additive increase) via: below for the congestion window size. Timeouts due to dropped Increment = MSS x (MSS/CongestionWindow) packets have occurred at the instances in which there is a sharp CongestionWindow += Increment decrease (by ½) of the window size. This doubles CongestionWindow after a CongestionWindow of packets have been ACKed. 11/10/2011 1 of 5 6.3.2 Slow Start When a connection is first of the AdvertisedWindow. This burst would often started we want to increase ___________________________ Internet routers. CongestionWindow as rapidly Slow start is also used immediately after a timeout until the as possible to near its steady- window reaches ½ its size prior to the timeout (with slow start state value(s). Instead of the window is reset to 1 packet after a time out). The sizing increasing it linearly at start up, algorithm then switches to AIMD. it is _______________ each Notice the slow start intervals after a timeout in the graph of time all the packets sent in a congestion window size below. RTT are ACKed. Slow start increases the window more rapidly than additive increase. It is called slow start Bullets indicate timeout events. Horizontal lines at top correspond to packet transmission times. Verticals lines are times at which a packet(s) that eventually times out is first transmitted. because TCP would originally send out a burst of data the size 6.3.3 Fast Retransmit and Fast Recovery Notice the gaps in the horizontal lines on the graph on the When an out-of-order packet is previous slide. These represent intervals in which the sender has received the receiver sends a sent a window of data and is waiting for an ACK (a timeout __________________ ACK of eventually occurs). the last in-order packet. Fast ____________________ allows a sender to retransmit a lost When the sender sees three packet before it times out. Fast retransmit and fast recovery duplicate ACKs it resends the were not in the original TCP congestion control algorithm, but (presumed) dropped packet. were added later. 11/10/2011 2 of 5 Fast retransmit results in about a 20% increase in With fast recovery the window size is decreased by ½ after a fast ______________________. This is shown in the graph below. retransmit and the algorithm enters AIMD mode. The congestion window is now decreased when duplicate ACKs Slow start is used only after a timeout. The window size is reset are received (as well as when a timeout occurs). to 1 packet. Slow start is used until the window size reaches ½ its size before the timeout. At all other times the congestion window follows a pure ___________________ pattern. 6.4 Congestion-Avoidance Mechanisms 6.4.1 DECbit TCP uses congestion control. It relies on timeouts and duplicate In the Digital Network Architecture (DNA) network, DNA ACKs to detect when congestion is occurring and then decreases routers would set a bit (the _________________) when they the window size. were busy (the average queue length exceeded a threshold). The An alternative strategy would be to use congestion avoidance in receiver would copy the bit into its ACK. which the sender _______________ when congestion will occur At the sender, if more than 50% of the packets in the previous and reduces the rate before packets are discarded. Ideally congestion window had the DECbit set the window would be packets would never be lost due to congestion. decreased by 0.875. If not, the window would be increased by one packet. 6.4.2 Random Early Detection (RED) RED also requires special routers, but can be used with TCP. The probability P is a function of the queue length as shown RED routers monitor their queue length and ______________ below. notify the sender of congestion by dropping packets before It is also a function of the time since the last packet was dropped. congestion actually occurs. P __________________________ with time to prevent clusters If the average router queue length is below MinThreshold no of drops by distributing the drops over time. packets are dropped. If the length is above MaxThreshold all incoming packets are dropped. If the length is between the threshold values a packet is dropped with probability P. 11/10/2011 3 of 5 6.4.3 Source-Based Congestion Control There are a collection of congestion avoidance algorithms that A second algorithm looks for changes in both the RTT and the do not require special routers. They look for signs that some window _________________. If router's queue is building up and then throttle back to avoid (CurrentWindow – OldWindow) congestion. x One algorithm looks for an ____________________ in RTT as a (CurrentRTT – OldRTT) signal. AIMD is normally used but every two round-trip times it is positive the window is reduced by 1/8th. Otherwise, it is compares the current RTT to the average of the min and max increased by 1/8th. RTTs seen so far. If the RTT is greater, the window is reduced by 1/8th. A third algorithm looks for a _____________________ in A fourth algorithm, known as TCP ________________, throughput as a signal that congestion is occurring. compares the measured throughput to an expected value. Every RTT the congestion window is increased by one packet. The design of TCP Vegas is based on the observation (illustrated If the difference in throughput falls below a threshold the in the graphs on the following slide) that, prior to congestion, the window size is decreased by one packet. (This algorithm window size increases while the sending rate remains flat. effectively looks for a change in the slope of the throughput.) The difference (Diff) between the ExpectedRate and the ActualRate is compared to α and β thresholds (α < β). If Diff < α the window is increased linearly. If Diff > β the window is decreased linearly. TCP Vegas calculates an expected sending rate from: TCP Vegas congestion control. Top – congestion window. Bottom – expected (black) and actual throughputs. ExpectedRate = CongestionWindow/BaseRTT where BaseRTT is the minimum of all round-trip times. 11/10/2011 4 of 5 TCP __________________ is the name of the original TCP control algorithm. Linux allows the system administrator to congestion control algorithm (AIMD, slow start). TCP Reno choose which algorithm to use. TCP Reno is currently the added fast retransmit and recovery. default, but TCP Vegas can be selected. (See the tcp man page.) TCP Reno is currently the most widely used TCP congestion Explicit Congestion Notification (ECN) Explicit Congestion Notification (ECN) is a congestion a router to indicate congestion. Bit 7 is echoed back to the avoidance mechanism that is also an IETF standard. sender in the ACK. TCP responds to the setting of the ECN bit Bits 6 and 7 of the IP ______________ field are used. Bit 6 is the same way it responds to a dropped packet. set by the sender to indicate that it supports ECN. Bit 7 is set by In Class Exercises • Does Linux support ECN? If so, is it enabled by default? If it is supported and not enabled by default, how is it enabled? • What is the currently used congestion control algorithm on csserver? • Does Linux support TCP Vegas congestion avoidance? If so, how is it enabled? 11/10/2011 5 of 5