Network Management
advertisement
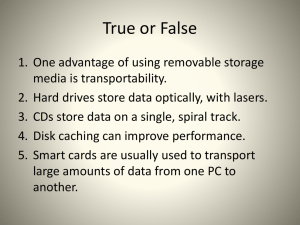
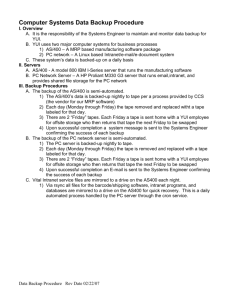
Network Management Semester 3, Chapter 8 Allan Johnson LAN Management This chapter deals mainly with the management of LANs. Although the content is not covered on the CCNA exam, it is covered on the Comp TIA Net+ exam. In addition, network management is when the real work begins for a net admin. Topics covered include: Documentation Security Network Performance Server Administration Troubleshooting Network Documentation Documentation Documenting the network, including: Cut sheet diagrams MDF & IDF layouts Server/workstation configurations Software installed Maintenance records Security & user policies ...is the most critical component of good network management. Documentation is also the least implemented component of network administration. MDF & IDF Layouts The Physical and Logical layouts of all wiring closets includes: physical location of rack mounts, equipment and servers patch panel labeling scheme for identifying cable terminations Configuration details of all equipment Server/Workstation Configurations Includes details about: Hardware specifications • Make & model • Number & type of drives • Cards installed Physical location & Logical addressing • IP and MAC address • Subnet • Topology Purchase date and warranty information Software & Maintenance Records Software listings include: All software installed on each computer The standard configuration used for each type of workstation Operating system information Maintenance records assist net admin to anticipate potential problems and include: All repairs and upgrades made to a computer Security & User Documents Physical Security How are MDFs & IDFs locked Who has access to MDFs & IDFs How are host devices protected (security cables, etc.) Soft Security User policies & rights outlining what is and what is not permissible on the network Password protection Firewall support Network Security Security Network security includes two major components: Controlling Access Data Protection and Recovery Access The network policy established during the documentation phase determines the criteria used to select passwords, such as: password length aging of passwords time of day access is allowed Acceptable Use Policies make sure users are aware of the company’s definition of what is allowed and not allowed on the network. It also normally includes consequences for violation of the policy. Data Recovery Data recovery, the second component of security, involves protecting data from loss Methods for protecting data include: Tape backup Fault tolerance Controlling Environmental Factors Power Conditioning Preventing Virus Corruption Tape Backup Magnetic tapes are the most popular media used for backing up data because of the cost and capacity. They are much cheaper than removable hard drives Tape backups record and restore data sequentially. This can make it difficult to find a particular file. However, tape backups are used to fully restore all lost data. Most Tape Backup systems use an archive bit set to on or off. If the bit is on, then the data has been changed since the last backup. Types of Tape Backup Systems Several options are available when using tapes. Full backup--all files are backed up periodically Incremental and Differential backups--uses an archive bit to determine if a file has been created or modified since the last full backup Copy backup--backs up user selected data to tape Daily backup--backs up data created or modified for that day Fault Tolerance Fault tolerance involves establishing redundancy techniques to keep a system up and running when a failure occurs. RAID (Redundant Array of Inexpensive Disks) RAID 0--stripes data across multiple disk; no redundancy RAID 1--(mirroring) provides redundancy by writing all data to two or more drives RAID 2--no longer used because of expense RAID 3/4--stores parity on one disk; 3 stripes at the byte level and 4 stripes at the block level across remaining disks. RAID 5--similar to 3/4 but stripes data with parity across multiple drives. Requires at least 3 drives. 5 drives is ideal. Environmental Factors Electrical Static Discharge can approach 20,000 volts and fry sensitive computer components Protect against by grounding yourself using grounding strap before working on computers Dust and dirt should be avoided. Periodically clean keyboards, monitors, and towers Avoid excessive heat Follow TIA/EIA 568A standards to avoid EMI and RFI noise For example, Shielded Twisted Pair (STP) cable is a possible solution to prevent EMI/RFI corruption of data. Power Conditioning Power conditioning is the process of implementing procedures to control the power supplied to your network. They include: Isolating Transformer--to control voltage spikes and high frequency noise Regulators--to maintain a constant level of voltage Line Conditioner--an isolating transformer/regulator combination. Uninterruptible Power Supply--maintains a charged battery to supply voltage to devices in the event of a power failure. Software Viruses Preventing software viruses is the final topic under network security. Types include: Worm--a program that spreads across computers and usually reproduces copies of itself in a computer’s memory Virus--a program that usually has a negative effect on executable programs Trojan Horse--destructive program disguised as a game, utility or other application Preventing viruses includes... Know where your data is coming from Avoid allowing others to use floppies on your computer Maintain updated virus checking software Network Performance Monitoring the Network Part of documenting the network is establishing baselines for the various performance issues including... Bandwidth utilization Collision counts Broadcast traffic A baseline sets the acceptable performance of the network, but must be updated as the network is updated or expanded. Server Administration Types of Networks Peer-to-Peer Networks Also known as a Workgroup Network, it is designed for a small number of users. No more than 10 devices should be on one peerto-peer network. Advantages: relatively easy to configure, users control resources, no dedicated server needed Disadvantages: no central management Client-Server Networks Uses a dedicated server running a NOS to control resources and manage the network. Types of Client-Server NOSs UNIX Open standard with proprietary versions offered by HP, IBM, and Sun (among others) as well as a free versions (FreeBSD and Linux). Multi-user, multi-tasking environment using NFS security. Kernel based which isolates the hardware layer from improperly operating applications. Types of Client-Server NOSs NetWare various versions as discussed in Ch. 7 uses two file services: FAT and DET Windows NT uses domains to control services with a Primary Domain Controller and Backup Domain Controller Similar to UNIX except uses a different file system structure Network Troubleshooting Scientific Method Network troubleshooting is a systematic process that uses the scientific method: 1. 2. 3. 4. 5. 6. Identify the network/user problem Gather data about the network/user problem Analyze data and come up with possible solutions Choose and implement best solution Evaluate solution’s success and modify data collected, if necessary If problem still exists, return to Step 3. Typical Troubleshooting Scenario 1. 2. 3. User calls and says he can’t access the network (problem identified). Gather data by asking the user questions, checking logs, and hardware configurations. Analyze the data collected to determine possible solutions. Check the physical layer by pinging the user. If unsuccessful, ping the NIC from the the user’s computer using the loopback address: 127.0.0.1. Continue to ping along the network to find problem. If no problem, then check software. Typical Troubleshooting Scenario 4. 5. Implement the best solution to solve the problem. Evaluate the implemented solution to see if the problem has been solved. If not, return to Step 3.